WordPress is the world’s most popular Content Management System with millions of websites using it. Its popularity makes it an easy target for hackers and malicious users alike — creating scripts to compromise WP websites and hampering WordPress security is a lucrative game.
As such, it is not uncommon for us to see several of our clients’ WordPress-powered sites getting compromised every now and then. Most of the time, the cause is something very basic — an out of date plugin, a bad theme, or a poorly-secured database.
More often than not, the problem arises due to the fact that WordPress, as easy to use as it might be to setup and use, does not come with the most fool-proof security settings. If you are a WordPress user yourself, this might sound an alarm to you. However, there isn’t much cause of concern as WordPress can easily be hardened to keep malicious intent at bay.
5 Tips for Enhanced WordPress Security
In this article, we will be taking a look at the top five WP security issues that you should address. So without wasting any additional time, let’s get started!
1. Installing Security Plugins
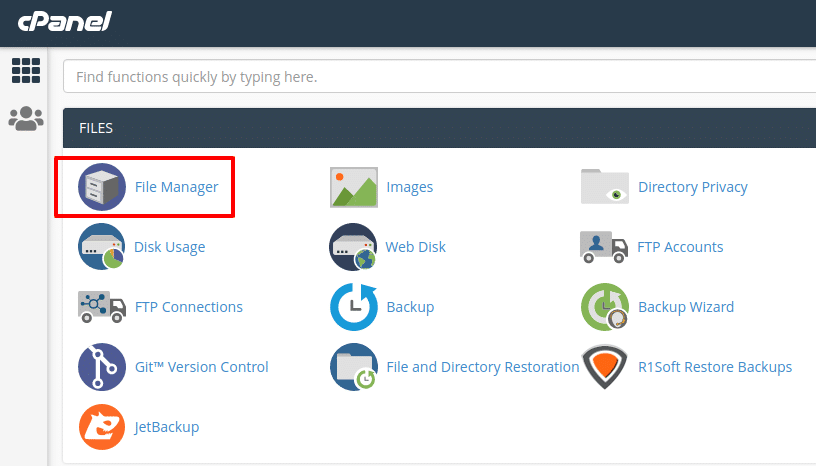
The first and most important step that you should take right after installing WordPress is to set up a security plugin. As robust and reliable as WordPress might be, it unfortunately does not come with a lot of security-focused features. To fix that, we need to configure and activate a WordPress security plugin.
WordFence Security is our standard recommendation when it comes to WordPress security plugins. The free version does its job fairly well and comes loaded with a plethora of features, such as real-time monitoring, brute force protection, virus scanning, database hardening, and more.
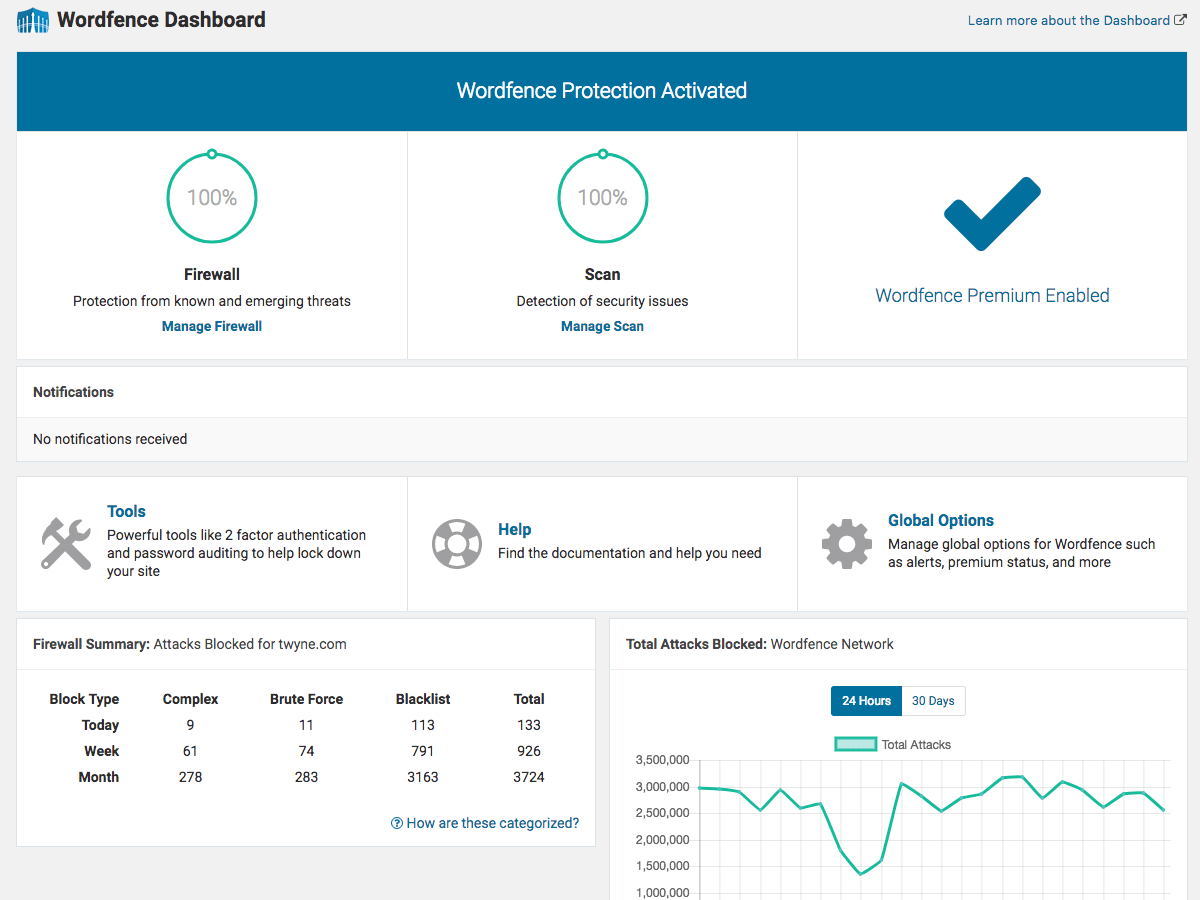
WordFence Dashboard
Another good choice for a WP security plugin is Sucuri Security. This particular plugin also offers a good set of configuration options, but its free version does not have a real-time firewall to block malicious users from accessing your site.
2. Changing Database and Table Prefixes
By default, WordPress adds the prefix wp_ to its database and tables. When you install WP via a script installer (such as Softaculous, that comes free with all our hosting plans and lets you install 250+ scripts in no time), the database prefix is often retained as wp_ itself.
This is an open invitation to malicious users, as they can inject malware in your database or, more commonly, access your user credentials remotely since the database and table prefix is easy enough to guess.
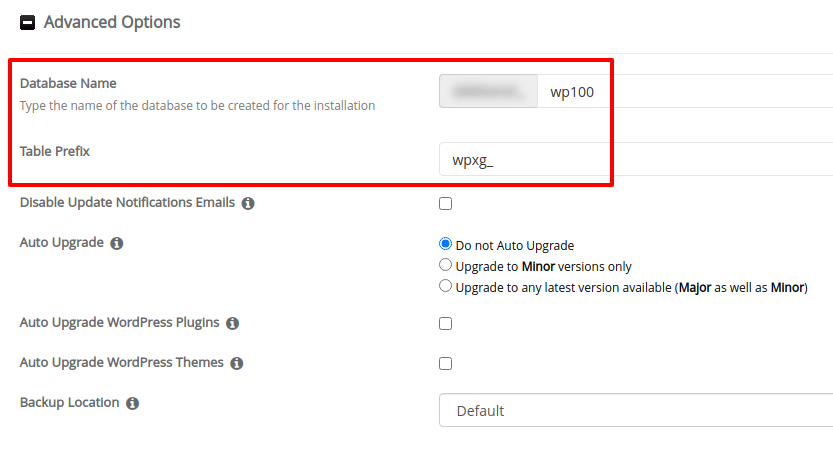
Changing the wp_ Prefix in Softaculous
The solution? Simply get rid of the wp_ prefix when installing WordPress and specify a custom prefix for the tables as well as the database. Softaculous lets you do that with ease.
3. Blocking Code Execution in Uploads Directory
The wp-content/uploads folder is where your uploads, such as images, videos and other media files, reside. As such, this particular folder is accessed by several plugins and themes — for showing thumbnails of your blog posts, videos, and so on.
It is a good strategy to prevent code execution in the uploads directory. Generally, malicious or compromised plugins tend to execute their code in the wp-uploads directory, often disguising it as a user-uploaded media file. If you have blocked code execution in the wp-content/uploads folder, you can minimize such risks and safeguard your site.
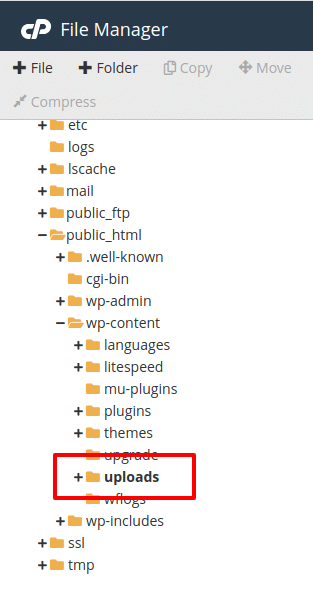
To do that, the simplest and easiest way is to use a custom .htaccess file. First up, log on to your cPanel and head to the File Manager.
Next, navigate to the wp-content/uploads directory. Make sure that dot files (hidden files) are visible.
If it doesn’t already exist, create an .htaccess file therein. Paste the following code in the .htaccess file, and save it:
<FilesMatch "\.(?i:php)$"> <IfModule !mod_authz_core.c> Order allow,deny Deny from all </IfModule> <IfModule mod_authz_core.c> Require all denied </IfModule> </FilesMatch>
That’s all. You have disabled code execution in that particular folder.
You can repeat the same process for various other directories, but the uploads folder is the most common place that needs to be secured. Furthermore, if you disable code execution in a plugin folder, you may end up breaking your site. However, the wp-content/uploads directory is never used for executing PHP code and as such, disabling such code execution in that particular directory cannot adversely impact your site.
4. Preventing Brute Force Attacks
A brute force attack means a malicious user (generally a bot created for this very purpose) is trying to access your WP admin panel by guessing your password. Even though SQL injections and poorly configured databases are big risk factors, brute force attacks still remain the most common reason for a hacked WP site.
There are various steps that you can take to nullify the risks of a brute force attack:
- To begin with, ensure that you use a difficult to guess password, and change it often. This applies especially to your administrator accounts.
- Never use the username ‘admin’; instead, use a more obsolete username for the admin account.
- Most WP security plugins, such as WordFence Security and Sucuri Security named above, can safely prevent brute force attacks and also block malicious user IPs altogether. More importantly, such plugins can send you login alerts for every admin or non-admin user that signs in, thereby keeping you informed about activity on your site.
- You may also try replacing your wp-login page with something else. WPS Hide Login lets you rename the login page to anything of your choice without having to touch code. Keeping the login page URL discrete and well-concealed is a sound security practice.
Another key aspect that can go a long way in preventing brute force attacks is to add two-factor authentication to your site. 2FA as it is commonly called is “what you have and what you know. ” You know your password and you have a unique one time code via your authenticator app. You can do so by means of a plugin such as Google Authenticator that helps you validate logins via phone.
5. Managing User Roles for WordPress Security
This one is relatively easier — you do not need to give admin privileges to everyone.
Simply put, you should keep your administrator accounts separate from your content or editor accounts. This way, accidentally leaving a security loophole is generally ruled out.
Conclusion
So there you have it — five simple WordPress security tips that you can implement to keep malicious users and hackers at bay.
You can also read our guide to WordPress security plugins for additional details related to WP plugins.
If you have any web hosting questions please feel free to reach out to us. We're happy to help.