In this document, we will show you to disable the SSH root login to your server.
A major security hole is to allow direct root access without any restrictions. This is an open door for hackers. They can attempt to brute force your root password and potentially get access to your server if the password can be guessed.
Quick Steps:
- Login to the server via SSH.
- Open the file “/etc/ssh/sshd_config” in any of your favorite text editors.
- Find the section in the file containing the line with “#PermitRootLogin yes” in it.
- Uncomment and change it to “PermitRootLogin no”.
- Save the file and exit.
- Restart the sshd service.
Disabling SSH Login for Root
The first step is to login to the server. Please note that you need to get more than one terminal access to the server because in case we lost one connection you can recover and get access to the server with the other one.
Open the SSH configuration file with your text editor.
vi /etc/ssh/sshd_config
Locate the directive PermitRootLogin,
#PermitRootLogin yes
Uncomment the line and change the directive No.
PermitRootLogin no
Save and close the file. Restart the SSH daemon to save the changes by executing one of the commands below,
/etc/init.d/sshd restart
systemctl restart sshd
service sshd restart
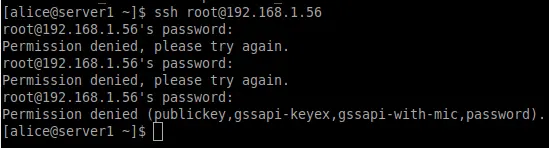
From now on, any attempt to SSH to the server with the root account will be automatically denied.
Conclusion
The SSH login for the root account has been successfully disabled on your server. You will not be able to SSH to server with the root account.
If you have any web hosting questions please feel free to reach out to us. We're happy to help.
Our Guiding Principles