In this post, we will be learning how to clean up a hacked WordPress site.
Even the best and most secure websites can get hacked. It can happen to anyone of us; even if we take the best WordPress security measures, our sites can still be compromised. This is pretty much like our own physical health — even after taking the best precautions and having a strong immune system, we might catch a cold at times.
How to Clean a Hacked WordPress Site?
With that said, how can we handle a hacked WordPress site? Is there something that can be done to fix it? This article will answer all such questions.
The Importance of Regular Backups
This is more of a precautionary measure than a cure. However, if you have regular backups of your content with you, life becomes much easier. You can simply restore from a backup and get started right away. In this manner, you can clean your infected website in no time.
Generally, your web hosting provider takes regular backups of your site. However, you should also consider keep backups of your own on a remote location. If your website has been compromised or hacked, simply delete it and restore from a backup. You might end up losing some recent data, but this is the fastest and easiest way of recovering a hacked WordPress site.
Scan for Malware
Whether or not you restore from a backup, you first need to know what exactly is the cause behind the issue. A hacked WordPress site is generally used to host malware or phishing scams. This can hide itself in a variety of ways and you need a proper virus scanner.
Simply ask your web hosting provider to run a virus scan on your hosting account. In this manner, files that are outside of your WordPress installation will also be scanned. If there are issues found, work with your web host to sort them. Generally, such virus and malware scans are thorough and you will discover the problems that have resulted in the hacked WordPress site.
Scanning WordPress
If you have implemented a decent WordPress security strategy, you might already be using a plugin such as Wordfence Security to scan your website at regular intervals. However, for a hacked WordPress site, the best scanning plugin is Exploit Scanner.
Exploit Scanner is currently maintained by Automattic, the parent company behind WordPress. It scans your WP files as well as your database records such as comments and other data for suspicious activity. This plugin can also compare your plugins and themes for any recent changes against the official version. As such, if there is something wrong with your WordPress website, Exploit Scanner can easily locate it.
However, note that the Exploit Scanner WP plugin does not fix anything. It only scans your files and tells you about the malware and issues with your site.
Cleaning Up WordPress
Generally speaking, your image files and other media content is not affected by malware. As a result, you mostly need to fix your WordPress core files. Following that, you should install official copies of your themes and plugins afresh.
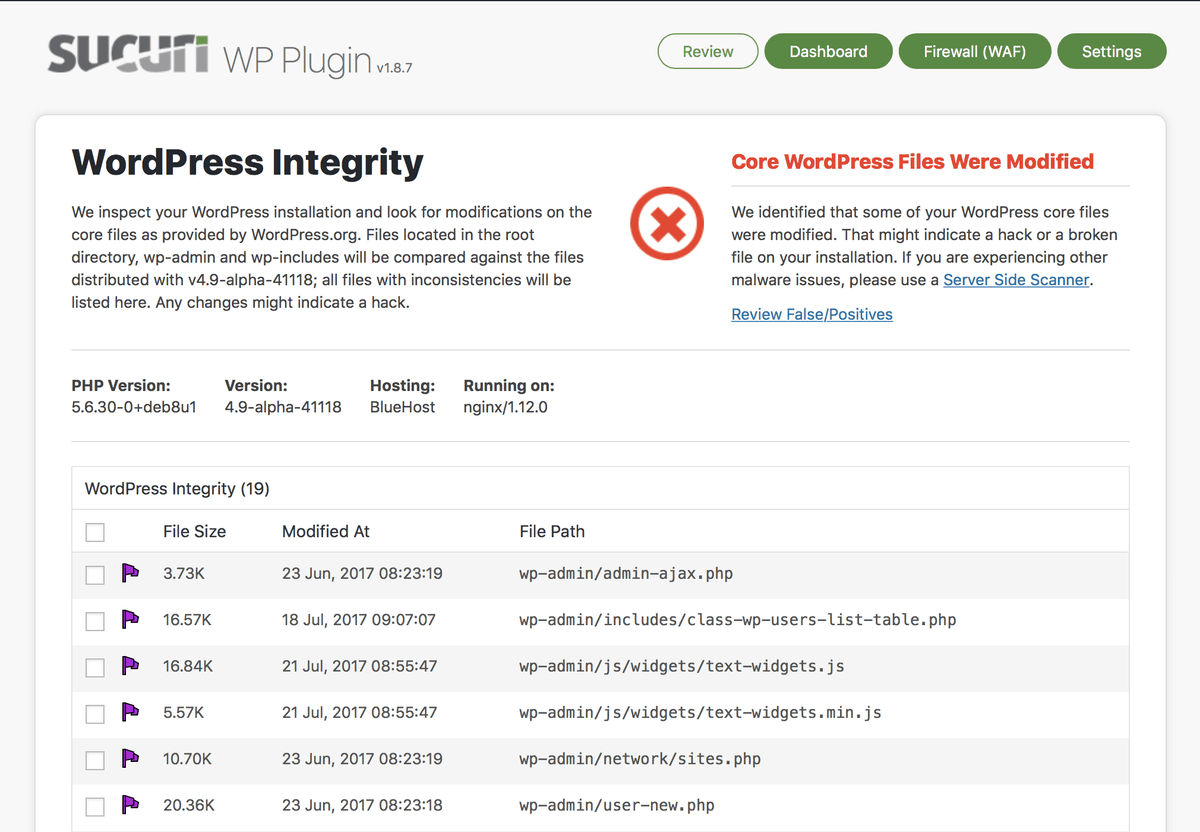
Sucuri Security lets you scan your WordPress files and restore the official versions in case any undesirable change is detected. Alternatively, you can access your site via FTP and overwrite by uploading fresh copies of WordPress core folders. If you are using FTP, be very sure not to overwrite the configuration files of WP — otherwise your website will not be able to connect to the database.
Bear in mind two simple things:
- Look out for any hidden files (plugins such as Exploit Scanner and Wordfence Security can tell you about non-WordPress files in WP core folders)
- In your wp-uploads directory, see if any .php files are present. Ideally, PHP code execution does not belong in the Uploads folder. Sucuri Security as well as Wordfence Security can block code execution in wp-uploads directory.
Fix Your Reputation
Now that you have restored clean files on your site, you probably must be good to go. However, there is one rather big step that is yet to be taken care of.
Almost all internet data firms and search engines, such as Google, maintain a malware and infected websites’ list. This list is ever expanding. If a malware or suspicious activity is detected on your site, your website will be blacklisted. Once you have cleaned your site, you need to get yourself removed from the blacklist.
While all such firms claim that removal from the blacklist is automated, it is rarely so. You automatically get on the blacklist if you have a hacked WordPress site. But you do not automatically get off the list once you have cleaned your site.
The process is simple: you need to manually contact each of them and request removal from the list. Once your website is scanned and proven to be free from malware, your domain will be removed from the blacklist.
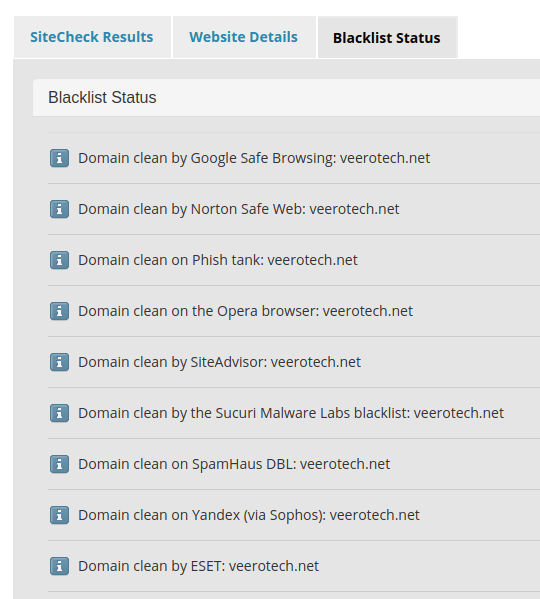
Here is how to do it: go to Sucuri SiteCheck. Use the free tool to diagnose your domain. Under the Blacklist Status tab, see if your domain name is blacklisted on any of the lists. For each of the list where you find your domain name unclean, click the button for details. Thereafter, simply contact the concerned blacklist site and request removal.
Note that you should do this only AFTER you have cleaned your website. Also, it takes a few days to be removed from the blacklist, so you need to be patient.
Conclusion
Once you have cleaned up your hacked WordPress site, try to make sure it never happens again.
To do that, keep your WP and plugins as well as themes updated. Plus, make sure you indulge in good practices for both WordPress plugins and themes. Also, it is a good idea to optimize and harden your WordPress website right during WP installation.
Up Next in the Series:
WordPress Optimization Part 7: Which WordPress SEO Plugin Should You Use?
If you have any web hosting questions please feel free to reach out to us. We're happy to help.